Risk management best practices for 2026 compliance
- Леонид Ложкарев
- Mar 6
- 10 min read

Choosing the right risk management practices in 2026 is more complex than ever. AI-driven threats, evolving regulations, and interconnected operational risks demand a strategic approach that balances compliance, resilience, and practicality. This article explores essential frameworks, emerging AI governance, cybersecurity strategies, and operational risk management to help you build a robust, audit-ready program tailored to your organization’s needs.
Table of Contents
Key takeaways
Point | Details |
Integrated approach required | Effective 2026 risk management combines traditional frameworks, AI governance, continuous monitoring, and cybersecurity resilience. |
NIST RMF and ISO 31000 remain foundational | These frameworks provide structured, auditable processes essential for compliance and regulatory alignment. |
AI governance is non-negotiable | Continuous AI system inventory, risk assessment, and enterprise-wide accountability address emerging technology threats. |
Cybersecurity must evolve | Extend Zero Trust to human identity layers and adopt continuous control testing to counter sophisticated attacks. |
Tailor practices to context | Select best practices based on organizational size, regulatory obligations, and specific AI risk exposure. |
Selection criteria for evaluating risk management best practices in 2026
Before adopting any risk management practice, you need clear criteria to evaluate its fit for your organization. The threat landscape in 2026 is fundamentally different from even two years ago, with AI-enabled attacks and fragmented regulations creating new compliance challenges.
Effective selection criteria include framework alignment, continuous monitoring, AI risk governance, regulatory compliance, and operational scope. Here’s what matters most:
Framework alignment: Does the practice integrate with recognized standards like NIST RMF or ISO 31000 to ensure audit credibility?
Continuous monitoring capability: Can you dynamically assess and respond to risks as they evolve, rather than relying on annual snapshots?
AI risk governance: Does the approach address emerging AI threats, including generative AI misuse and adversarial attacks?
Regulatory compliance: Will it help you meet evolving U.S. federal and sector-specific requirements?
Operational scope: Does it cover cyber, operational, and supply chain risk vectors comprehensively?
These criteria form the foundation for evaluating every practice discussed in this article. Understanding the role of risk assessment in your overall compliance strategy helps you prioritize which criteria matter most for your organization.
Risk management frameworks essential for compliance
Two frameworks dominate the risk management landscape in 2026 because they provide structured, repeatable processes that auditors and regulators recognize.
The NIST RMF is a 6-step integrated process widely used across federal agencies and private sector organizations. These steps are:
Prepare: Establish organizational context and risk management priorities
Categorize: Classify information systems based on impact levels
Select: Choose appropriate security controls from NIST SP 800-53
Implement: Deploy controls and document implementation details
Assess: Evaluate control effectiveness through testing and review
Authorize: Make risk-based decisions on system operation
Monitor: Continuously track control performance and emerging threats
ISO 31000 takes a broader view, expanding risk concepts beyond traditional probability and impact. It applies to any organizational objective, not just information security, making it valuable for enterprise-wide risk management.
Formal annual risk assessments must be documented per NIST SP 800-30 guidance. These assessments cover threat sources, vulnerabilities, likelihood ratings, and potential business impact. The documentation serves dual purposes: it guides risk treatment decisions and provides evidence for audits.
Framework | Primary Focus | Best For |
NIST RMF | Information security and system authorization | Federal contractors, regulated entities, cybersecurity-focused programs |
ISO 31000 | Enterprise-wide risk management principles | Organizations seeking holistic risk governance across all objectives |
NIST SP 800-30 | Detailed risk assessment methodology | Comprehensive threat and vulnerability analysis |
Both frameworks emphasize continuous improvement and integration with organizational processes. They provide the structure needed to demonstrate compliance while allowing flexibility in implementation.
Pro Tip: Start with NIST RMF if you have specific cybersecurity compliance obligations, then layer in ISO 31000 principles as your program matures to address broader operational and strategic risks.
The ISO 31000 risk management overview training can accelerate your team’s understanding of how these frameworks complement each other. Building competency in both approaches gives you flexibility to address diverse stakeholder requirements.
Integrating AI risk governance into enterprise risk management
AI risks represent the fastest-growing threat category in 2026. Traditional risk frameworks weren’t designed for the unique challenges posed by machine learning models, generative AI, and autonomous systems.

AI governance requires ongoing inventory, risk assessments, and enterprise-wide accountability to manage emerging threats effectively. Start by cataloging every AI system your organization uses, including third-party tools with embedded AI capabilities. Many organizations discover shadow AI deployments during this inventory phase.
Once you’ve identified AI systems, assess risks in these areas:
Data privacy and security: How does the AI handle sensitive information? Can training data be extracted through prompt injection?
Bias and fairness: Does the model produce discriminatory outputs that could create legal or reputational risks?
Adversarial attacks: How vulnerable is the system to manipulation through carefully crafted inputs?
Regulatory uncertainty: Which emerging AI regulations apply to your use cases?
Operational dependency: What happens if the AI system fails or produces incorrect outputs?
Socialize AI risk assessments across teams to build accountability. IT, legal, compliance, and business units must all understand their roles in managing AI risks. This cross-functional approach prevents gaps where risks fall through organizational silos.
Pro Tip: Create a lightweight AI risk register that non-technical stakeholders can understand. Use clear language to describe risks and map them to existing enterprise risk categories to demonstrate how AI risks connect to familiar concerns.
Integrating AI governance into your broader compliance management finance processes ensures these new risks receive appropriate resources and oversight. The goal is to manage AI risks proactively rather than reactively responding to incidents.
Adopting advanced cybersecurity and monitoring practices
Static security controls no longer provide adequate protection against sophisticated threats in 2026. Your cybersecurity practices must evolve to address AI-enabled attacks and increasingly creative adversarial tactics.
Continuous testing of NIST-aligned controls improves security rigor beyond annual assessments. Rather than checking compliance boxes once a year, implement automated testing that validates control effectiveness weekly or even daily. This approach catches control drift before it creates exploitable vulnerabilities.
Zero Trust must extend to human identity to counter AI impersonation. Deepfake audio and video can now fool traditional verification methods. Consider:
Multi-factor authentication with behavioral biometrics: Analyze typing patterns, mouse movements, and other subtle indicators
Out-of-band verification for high-risk transactions: Confirm sensitive requests through a separate communication channel
AI-powered anomaly detection: Identify unusual access patterns that may indicate compromised credentials
Regular security awareness training: Help employees recognize AI-generated phishing and social engineering attempts
Integrating cyber and fraud risk monitoring creates a more complete threat picture. Financial fraud and cybersecurity incidents often overlap, especially in attacks targeting payment systems or customer accounts.
“Over 1,800 API keys were exposed by autonomous AI agents in recent research, demonstrating how AI systems can inadvertently create new attack vectors while attempting to solve problems.”
This statistic highlights why traditional security models struggle with AI systems. The technology moves faster than security controls can adapt, requiring continuous vigilance.
Pro Tip: Deploy deception technologies like honeypots and honeytokens to detect attackers early. These tools provide high-confidence alerts with minimal false positives, helping security teams focus on genuine threats.
Understanding cybersecurity risks in depth helps you prioritize which advanced practices deliver the most value for your specific threat profile. The role of audit committees in 2026 cybersecurity oversight has expanded significantly, making it essential to communicate security posture effectively to governance bodies.
Addressing operational and supply chain risks
Operational resilience extends far beyond cybersecurity. In 2026, digital and geopolitical shifts compress risk horizons while supply chain concentration heightens disruption potential.
Supply chain risks have become more acute as organizations rely on fewer suppliers for critical components. A single supplier failure can cascade across multiple industries, as we’ve seen repeatedly in recent years. Geographic concentration adds vulnerability, with regional disruptions affecting global operations.
Key operational risk considerations include:
Third-party dependency mapping: Identify single points of failure in your supplier network and develop contingency plans
Technology concentration risk: Evaluate reliance on specific cloud providers, software platforms, or infrastructure vendors
Geopolitical exposure assessment: Understand how trade restrictions, sanctions, or regional instability could disrupt operations
Cascading failure modeling: Analyze how risks might propagate across interconnected systems and partners
Resilience testing: Conduct tabletop exercises and simulations to validate recovery capabilities
Operational risks increasingly intersect with technology and geopolitical factors. A cyberattack on a logistics provider, export restrictions on critical components, or natural disasters affecting key production regions can all trigger operational crises.
Building resilience requires holistic thinking. Don’t treat operational, cyber, and supply chain risks as separate domains. Model how they interact and compound each other. This systems thinking reveals vulnerabilities that traditional risk assessments miss.
The volatile environment demands continuous reassessment. Review operational risk profiles quarterly rather than annually to catch emerging threats early. Integrate compliance management finance considerations to ensure risk mitigation efforts align with budgetary realities.
Navigating regulatory compliance requirements in 2026
Regulatory expectations continue to evolve, with enforcement agencies taking harder stances on inadequate risk management. Understanding core compliance requirements helps you avoid penalties and maintain audit readiness.
Regulatory compliance necessitates documented risk assessments, encryption, role-based controls, incident response, and vendor risk management. These elements form the baseline for most U.S. regulatory frameworks, though specific requirements vary by sector.
Essential compliance practices for 2026:
Documented risk assessments: Update annually or when significant changes occur, covering threats, vulnerabilities, and business impact
Role-based access controls: Implement least privilege principles, regularly reviewing and certifying access rights
Data encryption: Protect sensitive data at rest and in transit using current cryptographic standards
Incident response plans: Maintain tested procedures for detecting, responding to, and recovering from security events
Workforce training: Conduct regular security awareness training with metrics tracking completion and effectiveness
Vendor risk management: Assess third-party security posture through questionnaires, audits, and continuous monitoring
CISA and NIST frameworks provide practical guidance that satisfies requirements across federal and private sector contexts. Aligning with these frameworks demonstrates due diligence and simplifies compliance when multiple regulations apply.
Audit readiness requires ongoing documentation. Don’t scramble to compile evidence when auditors arrive. Maintain a compliance repository with current policies, risk assessments, control tests, training records, and incident reports. This organization saves time and reduces audit stress.
The SOX compliance checklist for 2026 banking readiness illustrates sector-specific requirements, while the role of risk assessment remains foundational across all regulatory contexts.
Summary comparison and situational recommendations
Choosing the right combination of risk management practices depends on your organizational context. This table compares the approaches discussed:
Practice | Primary Benefit | Complexity | Best For |
NIST RMF | Structured cybersecurity compliance | Medium | Federal contractors, regulated entities, mid to large organizations |
ISO 31000 | Enterprise-wide risk principles | Low to Medium | Organizations seeking holistic governance across all risk types |
AI Risk Governance | Emerging technology threat management | Medium to High | Any organization using AI systems, especially customer-facing applications |
Continuous Control Testing | Real-time security validation | Medium | Organizations with dynamic threat environments or compliance obligations |
Zero Trust Enhancement | Advanced identity protection | High | High-value target organizations facing sophisticated threats |
Supply Chain Risk Management | Operational resilience | Medium | Organizations with complex supplier networks or geographic concentration |
Vendor Risk Management | Third-party security assurance | Medium | All organizations using cloud services or outsourced functions |
Situational recommendations:
Small to mid-sized organizations: Start with NIST RMF for structured cybersecurity, add basic AI governance if using AI tools, implement continuous testing for critical controls
Large regulated organizations: Adopt comprehensive ISO 31000 framework, full AI governance program, supply chain risk integration, advanced cybersecurity practices
AI-intensive operations: Prioritize AI governance and enhanced Zero Trust, integrate AI risks into enterprise risk register, invest in AI-specific security tools
Organizations with complex supply chains: Focus on third-party risk management, operational resilience testing, cascading failure modeling
Pro Tip: Regularly reassess your chosen frameworks and practices as threats and regulations evolve. What works today may need adjustment in six months as AI capabilities advance and new vulnerabilities emerge.
The ISO 31000 overview provides foundational knowledge applicable across contexts, while ISO 31000 in-person training offers hands-on practice implementing these principles.
Enhance your risk management skills with expert CPE training
Staying current with 2026 risk management best practices requires ongoing professional development. Compliance Seminars offers specialized CPE courses designed for audit, compliance, and risk management professionals navigating today’s complex environment.
Explore the 2026 CPE event calendar to find in-person training sessions in cities across the U.S. These events provide hands-on learning opportunities where you can apply frameworks like NIST RMF and ISO 31000 to real-world scenarios.
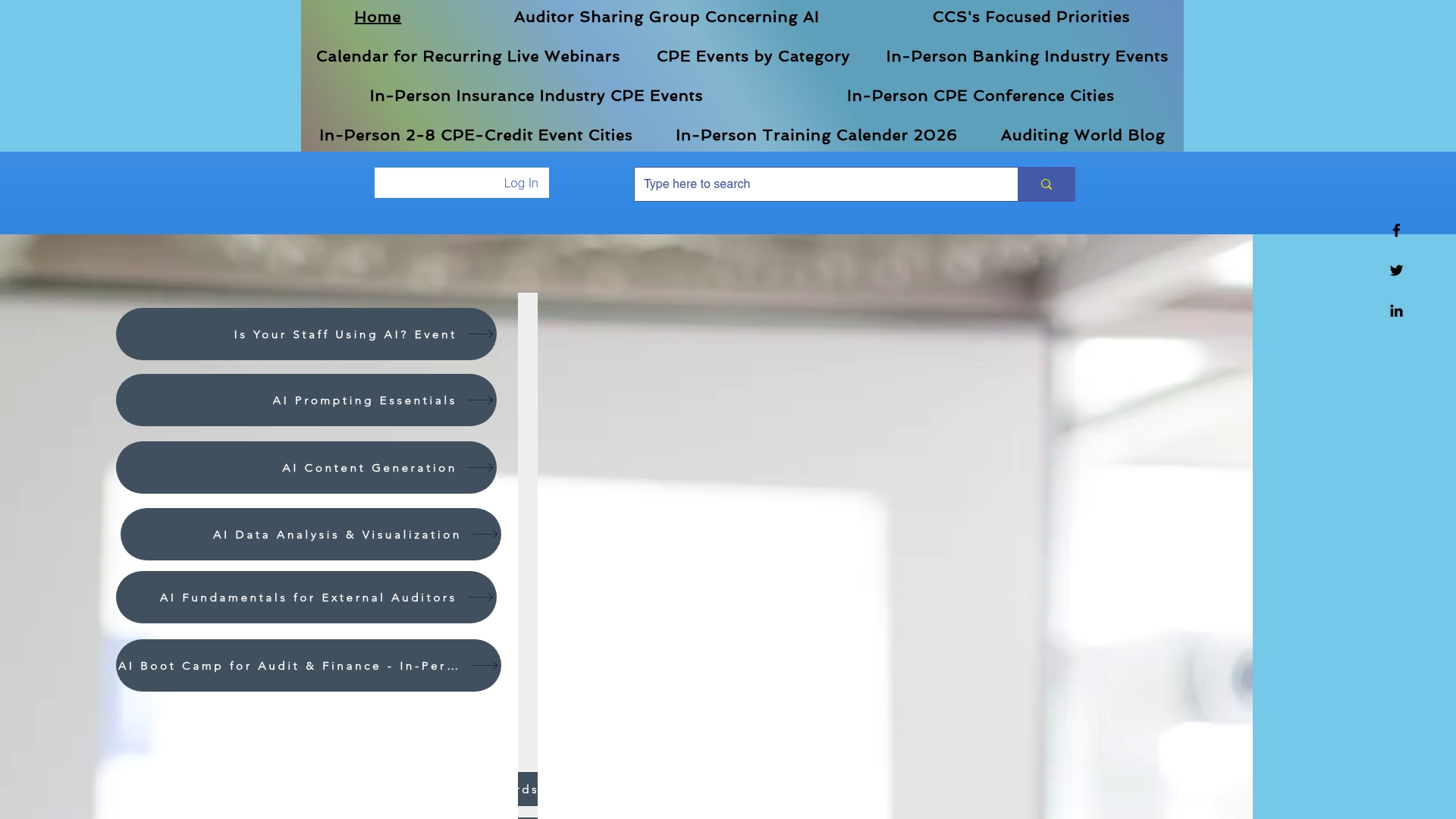
For flexible learning options, browse cybersecurity CPE events covering advanced topics like Zero Trust implementation and continuous control testing. If you prefer shorter sessions, internal auditor CPE webinars deliver focused content you can complete during your workday.
Expert instructors with Big 4 backgrounds guide you through practical implementations of the best practices discussed in this article. You’ll gain actionable skills to immediately enhance your organization’s risk management program while earning CPE credits that maintain your professional certifications.
Frequently asked questions
What are the key components of an effective risk management framework in 2026?
An effective framework integrates NIST RMF or ISO 31000 as the structural foundation, adds continuous monitoring capabilities for dynamic risk assessment, incorporates AI governance to address emerging technology threats, and ensures comprehensive coverage of cyber, operational, and supply chain risks. The framework must support documented, repeatable processes that satisfy regulatory requirements while remaining flexible enough to adapt as threats evolve.
How can organizations integrate AI risk governance into existing risk management programs?
Start by conducting a comprehensive inventory of all AI systems, including third-party tools with embedded AI capabilities. Perform risk assessments covering data privacy, bias, adversarial attacks, and operational dependency, then socialize results across IT, legal, compliance, and business teams to build shared accountability. Incorporate AI risks into your existing enterprise risk register using familiar risk categories to demonstrate connections with traditional concerns.
What cybersecurity practices are vital to counter AI-driven attacks in 2026?
Implement continuous testing of security controls rather than relying on annual assessments, extend Zero Trust architecture to human identity layers using behavioral biometrics and out-of-band verification, and integrate cyber and fraud risk monitoring for comprehensive threat detection. Deploy AI-powered anomaly detection tools and deception technologies like honeypots to identify sophisticated attacks early with minimal false positives.
What regulatory compliance steps are essential for risk teams in 2026?
Maintain documented annual risk assessments that cover threats, vulnerabilities, likelihood, and business impact, implement role-based access controls with regular access certification reviews, deploy encryption for sensitive data at rest and in transit, and develop tested incident response plans. Establish a robust vendor risk management program and align practices with NIST and CISA frameworks to satisfy requirements across multiple regulatory contexts while demonstrating due diligence.
Recommended
Comments