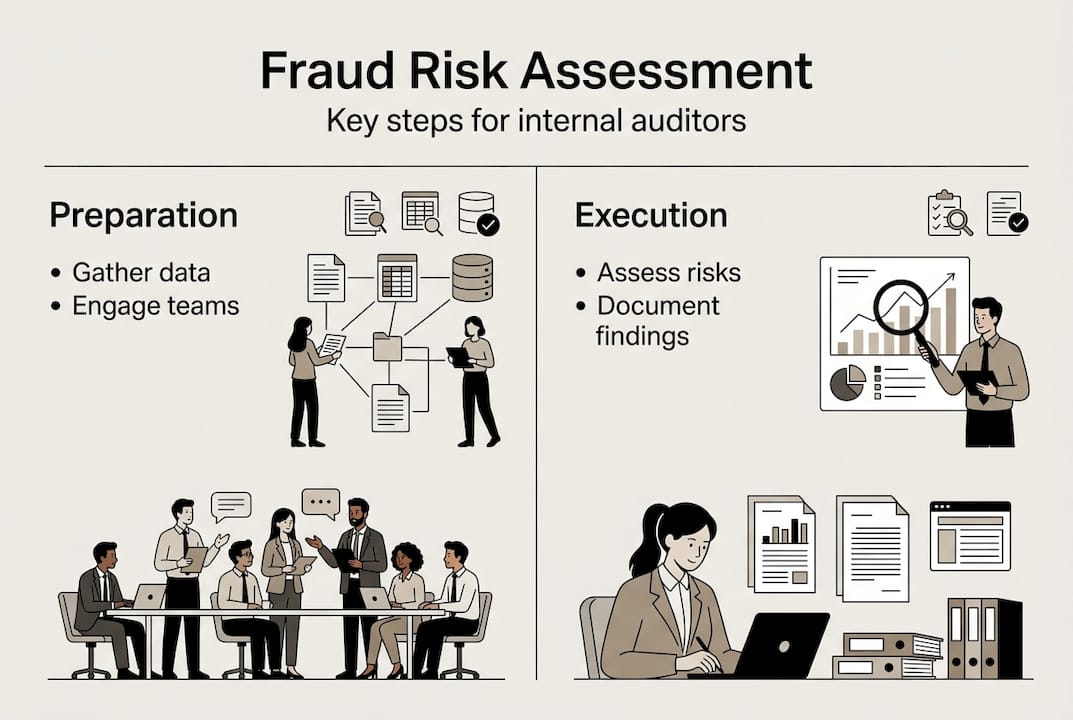
Fraud risk assessment process guide for internal auditors
- John C. Blackshire, Jr.

- 3 days ago
- 9 min read

You know the pressure of uncovering fraud risks before they become costly incidents. Internal auditors and compliance officers in finance face mounting expectations to identify vulnerabilities in increasingly complex operations. A structured fraud risk assessment approach enhances detection accuracy and prevents losses that could damage your organization’s reputation and bottom line. This guide walks you through a proven process to strengthen your fraud risk assessment capabilities, from preparation through verification.
Table of Contents
Key Takeaways
Point | Details |
Preparation foundation | Gather comprehensive financial and operational data from your systems to ensure the quality and completeness of your fraud risk assessment. |
Stakeholder engagement | Engage finance, legal, and compliance teams early to gain access to sensitive information and critical operational insights. |
Standardized tools | Use standardized risk assessment templates, interview guides, and data analysis scripts to capture risks, likelihood scores, impact ratings, and control evaluations. |
Define risk scenarios | Develop fraud risk scenarios covering asset misappropriation, corruption, and financial statement risk tailored to your organization. |
Preparation: What you need to conduct a fraud risk assessment
Before diving into your fraud risk assessment, you need the right foundation. Start by gathering comprehensive financial and operational data from your organization’s systems. This includes transaction records, journal entries, vendor files, employee expense reports, and system access logs. The quality of your assessment depends directly on the completeness of your data collection.
Engage early with your finance, legal, and compliance teams to gain critical insights and secure access to sensitive information. These stakeholders understand operational nuances that might indicate fraud risks you wouldn’t spot from documents alone. Schedule interviews with department heads to understand their processes and control environments. Pro Tip: Early stakeholder buy-in improves access to critical information and smooths the entire assessment process, reducing resistance when you need urgent data.
You must understand the regulatory landscape governing your organization. Familiarize yourself with applicable standards like the COSO Internal Control Framework, SOX requirements, and industry-specific regulations for banking or insurance sectors. Review your organization’s internal policies, code of conduct, and whistleblower procedures. This knowledge helps you identify compliance gaps that create fraud opportunities.
Prepare your documentation tools before starting fieldwork. Use standardized risk assessment templates that capture risk descriptions, likelihood scores, impact ratings, and control evaluations. Create interview guides with targeted questions about fraud risk indicators. Develop data analysis scripts or queries to identify unusual patterns in financial transactions.
Identify fraud risk indicators specific to the finance sector. These include:
Unusual account reconciliation delays or unexplained adjustments
Vendor master file changes without proper authorization
Duplicate payments or suspicious vendor relationships
Excessive override of system controls by privileged users
Rapid turnover in critical finance positions
Missing or altered source documents
Consider external threats too. Proxy detection is crucial for fraud prevention when assessing digital fraud risks. Understanding how fraudsters mask their digital footprints helps you design better detective controls.
Organize your preparation checklist:
Preparation Category | Specific Requirements | Timeline |
Data Collection | Financial records, transaction logs, system access data | Week 1-2 |
Stakeholder Engagement | Finance, legal, compliance, IT interviews | Week 2-3 |
Regulatory Review | COSO, SOX, industry regulations, internal policies | Week 1 |
Tool Preparation | Templates, interview guides, analysis scripts | Week 1 |
Risk Indicator Research | Sector-specific fraud schemes, red flag lists | Week 2 |
Execution: Step-by-step fraud risk assessment process
Now that you have prepared thoroughly, execute your assessment systematically. Follow these sequential steps to ensure comprehensive coverage and consistent evaluation.
First, define fraud risk scenarios relevant to your organization’s operations. Consider asset misappropriation schemes like cash theft, fraudulent disbursements, or inventory theft. Evaluate corruption risks including bribery, conflicts of interest, and kickbacks. Assess financial statement fraud through revenue recognition manipulation, expense concealment, or asset overvaluation. Tailor scenarios to your organization’s specific vulnerabilities based on industry, size, and control environment.
Second, collect evidence through multiple methods. Analyze financial data using analytical procedures to identify anomalies, trends, or outliers. Conduct interviews with process owners, management, and staff to understand control gaps and behavioral red flags. Review system configurations and access rights to spot segregation of duty violations. Examine documentation for completeness, authenticity, and proper authorization. A structured approach to fraud risk assessment enhances your detection accuracy.
Third, assess the likelihood and impact of each identified risk. Likelihood considers factors like control strength, management override capability, employee opportunity, and historical fraud incidents. Impact evaluates potential financial loss, reputational damage, regulatory penalties, and operational disruption. Use a consistent rating scale such as low, medium, high for both dimensions.

Fourth, prioritize risks using a scoring framework. Multiply likelihood and impact ratings to create a risk score. This helps you focus remediation efforts on the most significant threats. Document your rationale for each rating to support your conclusions.
Risk Assessment Method | Strengths | Limitations | Best Use Case |
Quantitative Scoring | Objective, data-driven, comparable across risks | Requires robust data, time-intensive | Large organizations with mature data systems |
Qualitative Assessment | Flexible, captures nuanced factors, faster | Subjective, harder to compare | Smaller organizations or initial assessments |
Hybrid Approach | Balances objectivity and judgment, comprehensive | Requires expertise to integrate methods | Complex environments with varied risk types |
Fifth, document your findings in a standardized report. Include an executive summary, detailed risk descriptions, likelihood and impact assessments, existing control evaluations, and recommended control enhancements. Present risks in priority order with clear action items and responsible parties. Your report should be actionable, not just informative.
Pro Tip: Use a comparison table to evaluate different risk assessment methodologies for your organization, considering factors like organizational maturity, data availability, and resource constraints before selecting your approach.
Consider how proxy detection tools help with fraud prevention in digital environments. Understanding technical fraud vectors strengthens your assessment of cyber-related fraud risks.
For comprehensive fraud risk coverage, examine what fraud risk means and how internal cases develop to inform your scenario development.
Verification and follow-up: Ensuring the fraud risk assessment’s effectiveness
Your assessment isn’t complete when you submit the report. Verification and ongoing monitoring ensure your work delivers lasting value and adapts to changing risks.
Perform periodic reviews of your assessment accuracy using updated data. Compare your risk predictions against actual incidents or near misses. If you rated a risk as low but it materialized, investigate why your assessment missed key indicators. This feedback loop improves your judgment and methodology over time. Schedule quarterly or semi-annual reviews to refresh your risk profiles.
Verify that management implements your recommended controls effectively. Don’t assume your suggestions translate into action without follow-up. Review control design documentation, test control operating effectiveness, and validate that controls address the identified risks. If management accepts the risk without implementing controls, document their rationale and ensure appropriate governance approval.
Use monitoring mechanisms to detect fraud on an ongoing basis. Implement or enhance whistleblower programs that provide confidential reporting channels. Deploy continuous monitoring analytics that flag suspicious transactions in real time. Conduct surprise audits of high-risk processes. Review system logs for unauthorized access or unusual activity patterns. Continuous verification and monitoring adapt fraud risk management to emerging threats.
Update risk profiles when organizational changes occur. New products, markets, systems, or business models introduce fresh fraud opportunities. Merger and acquisition activity creates integration risks and cultural challenges. Leadership changes may alter the tone at the top and control consciousness. Regulatory changes impose new compliance requirements. Don’t wait for your annual assessment cycle if material changes warrant immediate risk reevaluation.
Communicate results and improvements to stakeholders for governance transparency. Present findings to the audit committee, highlighting significant risks, control deficiencies, and management responses. Share relevant insights with operational management to build risk awareness. Provide training on new fraud schemes or control procedures. Effective communication turns your assessment into organizational learning.
Maintain a continuous improvement mindset in your fraud risk management approach. Stay current on emerging fraud schemes through professional networks, industry publications, and training programs. Benchmark your methodology against leading practices. Solicit feedback from stakeholders on how to make your assessments more useful. Leverage technology advances that enhance detection capabilities.
Key verification activities include:
Testing implemented controls for design and operating effectiveness
Analyzing fraud incident data to validate risk ratings
Updating risk scenarios based on industry trends and organizational changes
Reviewing whistleblower complaints for patterns indicating unassessed risks
Monitoring key risk indicators through dashboards and analytics
Conducting management interviews to assess control culture
Explore comprehensive risk assessment frameworks and practices that support ongoing verification activities.
Common challenges and best practices in fraud risk assessment
Even experienced auditors encounter obstacles that compromise assessment quality. Recognizing these challenges helps you proactively address them.
Data gaps represent a frequent challenge. Organizations often lack centralized data repositories, forcing you to compile information from multiple systems with inconsistent formats. Legacy systems may not capture the transaction details you need for analysis. Some data resides in spreadsheets or paper files rather than databases. Overcome this by establishing data requirements early, working with IT to extract and standardize information, and documenting limitations that affect your conclusions.
Limited stakeholder engagement undermines your assessment’s comprehensiveness. Busy managers may view your requests as burdensome rather than value-adding. Some departments resist sharing information due to territorial attitudes or fear of criticism. Build engagement by explaining how fraud risk assessment protects the organization and their departments. Frame your work as collaborative problem-solving rather than fault-finding. Schedule interviews at their convenience and respect their time.
Bias in risk ranking can skew your priorities. You might overweight risks in areas you understand well while underestimating threats in unfamiliar domains. Recent fraud incidents may inflate your perception of likelihood beyond statistical reality. Management pressure might influence your ratings to avoid uncomfortable findings. Combat bias by using structured scoring criteria, seeking peer review of your assessments, and maintaining professional skepticism regardless of management preferences.
Organizations lose an estimated 5% of annual revenues to fraud, making effective risk assessment a critical defense against financial losses and reputational damage.
Regular training and updated fraud typology knowledge benefit your ongoing assessments. Fraud schemes evolve as criminals adapt to new controls and exploit emerging technologies. Attend professional development courses focused on fraud examination, forensic accounting, and investigative techniques. Join industry groups that share fraud intelligence. Study case studies of recent fraud incidents to understand how schemes operated and what red flags appeared.
Leverage technology tools to detect anomalies and manage risks more efficiently. Data analytics software can process millions of transactions to identify outliers, duplicates, or unusual patterns that manual review would miss. Continuous auditing tools monitor transactions in real time rather than periodically. Visualization dashboards help you communicate complex risk information to non-technical stakeholders. Artificial intelligence can learn normal behavior patterns and flag deviations.
Best practices that strengthen your assessments include:
Rigorous documentation of your methodology, evidence, and conclusions
Clear communication tailored to your audience’s technical level and information needs
Defined escalation protocols for urgent risks requiring immediate attention
Independence from the processes and controls you’re assessing
Coordination with external auditors to leverage their work and avoid duplication
Integration of fraud risk assessment into enterprise risk management frameworks
Learn about internal controls to prevent corporate fraud to enhance your control evaluation skills.
Enhance your fraud risk assessment skills with expert training
Mastering fraud risk assessment requires continuous learning and skill development. Professional training sharpens your technical abilities and keeps you current on evolving fraud schemes and detection techniques.
Compliance Seminars offers specialized CPE courses designed for internal auditors and compliance officers who want to strengthen their fraud risk assessment capabilities. Our programs combine practical frameworks with real-world case studies, taught by instructors with Big 4 backgrounds and extensive fraud examination experience. Whether you prefer in-person intensive workshops or convenient webinars, we provide flexible learning options that fit your schedule.
Explore our 2026 CPE event calendar to find upcoming fraud-focused training in cities across the country. Our signature course on internal controls to prevent corporate fraud provides hands-on practice designing and testing anti-fraud controls. For auditors investigating suspected fraud, our forensic accounting program teaches investigative techniques and evidence gathering methods. These NASBA-approved courses earn you CPE credits while building skills that immediately improve your assessment effectiveness.
Frequently asked questions
What is the first step in a fraud risk assessment process?
The first step is gathering relevant financial and operational data while engaging critical internal stakeholders to understand potential fraud risks. This foundation ensures your assessment reflects actual organizational vulnerabilities rather than theoretical risks. Starting with comprehensive preparation improves the accuracy and credibility of your entire assessment.
How often should fraud risk assessments be updated?
Fraud risk assessments should be reviewed and updated at least annually to remain relevant. However, you should also update assessments when significant organizational changes occur, such as new business lines, major system implementations, leadership transitions, or regulatory changes. Continuous monitoring between formal assessments helps you identify emerging risks that warrant immediate attention.
What are common red flags identified during fraud risk assessments?
Common red flags include unusual transactions without business justification, missing or altered documentation, unexplainable accounting adjustments, and rapid staff turnover in finance roles. Other indicators include vendors with incomplete information, employees living beyond their means, override of automated controls, and reluctance to share information during audits. Identifying these early helps you focus audit efforts on the highest-risk areas.
Can technology improve the fraud risk assessment process?
Yes, technology such as AI and analytics tools significantly enhances detection capabilities and efficiency in fraud risk assessment. These tools process large transaction volumes to identify patterns and anomalies that manual review would miss. Auditors should leverage AI for detecting fraud to complement traditional techniques, creating a more comprehensive and proactive fraud risk management approach.
Recommended
Comments