Fraud detection process guide for auditors in 2026
- John C. Blackshire, Jr.

- 4 days ago
- 10 min read

Fraud schemes cost organizations billions annually, yet many auditors struggle to detect sophisticated fraud before significant damage occurs. Management override of controls remains a presumed significant risk in every audit, demanding specific procedures and heightened vigilance. This comprehensive guide walks you through a proven, standards-aligned fraud detection process that integrates PCAOB and AICPA requirements with cutting-edge data analytics. You’ll learn practical frameworks, advanced techniques, and expert strategies to strengthen your fraud detection capabilities and protect stakeholder trust.
Table of Contents
Key takeaways
Point | Details |
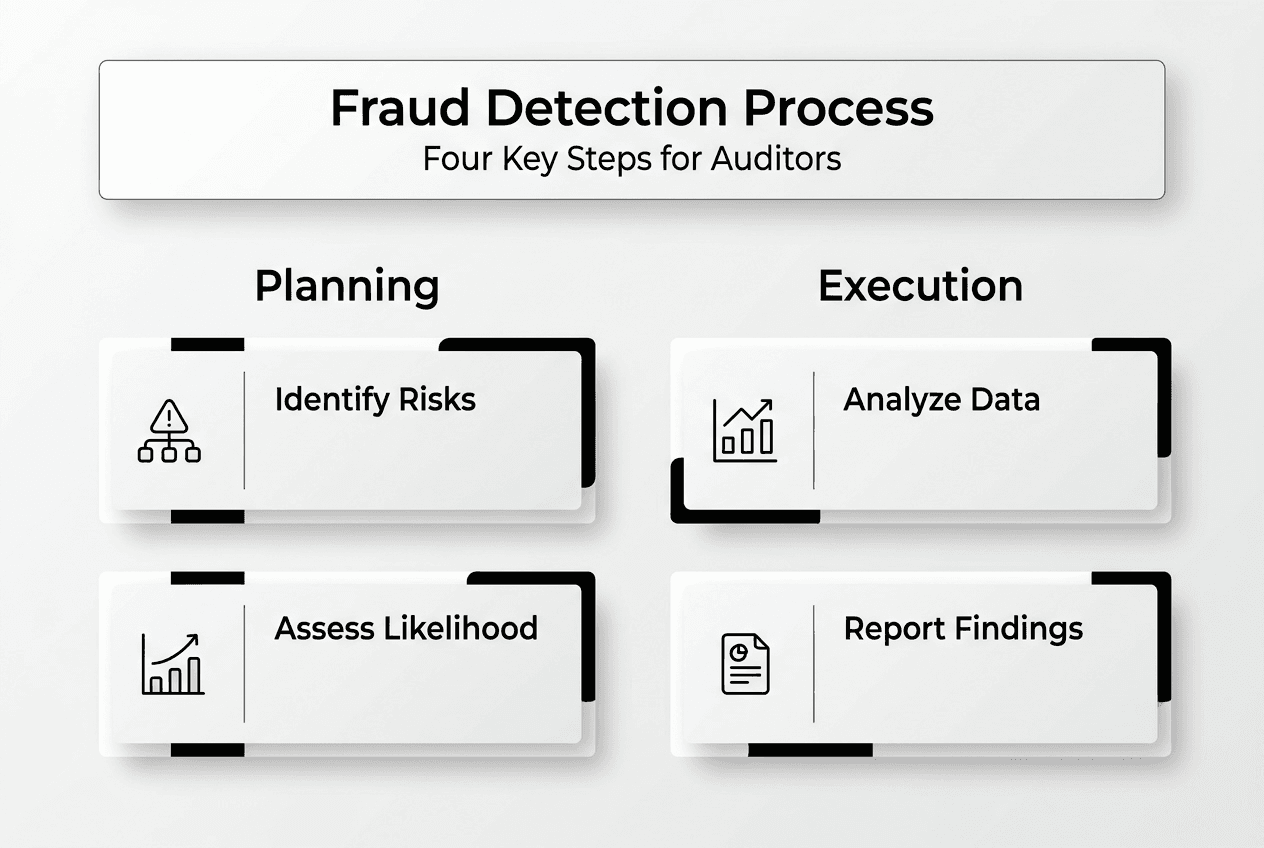
Structured four-phase process | Fraud risk assessment follows identification, assessment, response, and communication phases per AU-C 240 and AS 2401 standards. |
Advanced analytics boost accuracy | Machine learning models like Random Forest and XGBoost achieve over 95% detection accuracy compared to traditional methods. |
Framework integration ensures compliance | Combining PCAOB/AICPA standards with COSO principles creates a comprehensive, regulatory-compliant fraud detection approach. |
Verification and communication are critical | Enhanced testing procedures and transparent stakeholder communication complete the fraud risk management cycle. |
Continuous skill development matters | Ongoing training in emerging fraud schemes and detection technologies keeps audit teams effective and current. |
Understanding the fraud detection challenge
Auditors today face increasingly sophisticated fraud schemes that exploit technological advances and organizational complexity. Financial statement fraud, asset misappropriation, and corruption schemes have evolved beyond simple manipulation, incorporating layered transactions and digital concealment techniques. Traditional sampling and manual review methods often miss these complex patterns, leaving organizations vulnerable to material misstatements.
Management override of controls presents a particularly challenging risk factor. Senior executives can circumvent established controls, manipulate accounting estimates, or suppress unfavorable information without triggering standard detection mechanisms. This risk exists in every organization regardless of control strength, requiring auditors to maintain professional skepticism and apply specific testing procedures.
Traditional detection approaches face several critical limitations:
Manual sampling covers only small transaction populations, missing anomalies in unexamined data
Periodic testing creates gaps where fraud can occur between audit cycles
Standard analytical procedures may not identify subtle manipulation patterns
Resource constraints limit the depth and breadth of fraud-focused testing
A proactive, standards-based framework addresses these limitations systematically. Rather than reacting to discovered fraud, effective detection integrates continuous monitoring, advanced analytics, and risk-focused procedures throughout the audit process. This approach aligns with regulatory expectations while providing practical tools to identify fraud indicators before they escalate. Understanding key fraud issues for auditors helps prioritize detection efforts where risks are highest.
“The most effective fraud detection combines professional skepticism with systematic application of risk assessment procedures and data analytics. Auditors must look beyond compliance checklists to truly understand organizational vulnerabilities.”
Recognizing these challenges sets the stage for implementing a comprehensive detection process that addresses both regulatory requirements and practical effectiveness. The framework detailed in subsequent sections provides the structure and techniques needed to overcome traditional limitations and enhance fraud detection capabilities.
Preparing for fraud detection: frameworks and risk assessment
Effective fraud detection begins with thorough preparation grounded in recognized standards and frameworks. Fraud risk assessment follows a four-phase cycle comprising identification, assessment, response, and communication per AU-C 240 (AICPA) and AS 2401 (PCAOB). Integrating these auditing standards with the COSO Internal Control Framework creates a comprehensive approach that addresses both regulatory compliance and practical control effectiveness.
The four-phase cycle structures fraud detection systematically:
Phase | Key Activities | Expected Outcomes |
Identification | Brainstorming sessions, inquiry procedures, analytical reviews | Documented fraud risk factors and potential schemes |
Assessment | Evaluate likelihood and significance, consider controls | Prioritized fraud risks requiring audit response |
Response | Design and execute procedures addressing identified risks | Evidence supporting fraud presence or absence |
Communication | Report findings to management and governance | Stakeholder awareness and remediation plans |
The identification phase requires auditors to consider fraud opportunities across the organization. This involves understanding the business environment, industry-specific risks, and organizational pressures that might motivate fraudulent behavior. Team brainstorming sessions bring diverse perspectives to identify schemes that individual auditors might overlook. Inquiry procedures with personnel at various levels reveal control weaknesses and unusual transactions that warrant further investigation.

Assessment builds on identified risks by evaluating their significance and likelihood. Consider both quantitative factors like potential financial impact and qualitative factors such as reputational damage. Existing controls provide some mitigation, but auditors must assess whether controls adequately address specific fraud risks or whether gaps exist. This evaluation determines which risks require enhanced audit procedures beyond standard testing.
Integrating risk assessment for auditors with COSO principles strengthens the overall control environment. COSO’s five components (control environment, risk assessment, control activities, information and communication, monitoring) provide a holistic view of organizational fraud defenses. Auditors should evaluate how well these components function together to prevent and detect fraud, identifying weaknesses that increase organizational vulnerability.
Pro Tip: Smaller organizations may lack formal fraud risk assessment processes. Help them establish simplified but effective frameworks by documenting key risks, implementing segregation of duties where feasible, and establishing clear tone-at-the-top communications about ethical expectations. Even basic frameworks significantly reduce fraud opportunity when consistently applied.
Key considerations during preparation include:
Document all fraud risk factors identified, even those deemed low probability
Consider how management could override specific controls in your risk scenarios
Evaluate information technology controls that could be exploited for fraud
Review prior audit findings and industry fraud trends for relevant patterns
Understanding the role of risk assessment in overall audit strategy ensures fraud detection integrates seamlessly with other audit objectives. This preparation phase establishes the foundation for executing specific detection procedures with clarity about what you’re looking for and why certain risks merit heightened attention.
Executing fraud detection with data analytics and machine learning
Advanced data analytics transforms fraud detection from sample-based testing to comprehensive population analysis. Data analytics enhances detection through tools like Benford’s Law and machine learning models including Random Forest, XGBoost, and neural networks, which outperform traditional methods with accuracy exceeding 95%. However, challenges include data imbalance and model interpretability that auditors must address carefully.
Benford’s Law provides a foundational analytical technique. This mathematical principle predicts the frequency distribution of leading digits in naturally occurring datasets. Financial data that deviates significantly from expected Benford distributions may indicate manipulation or fabrication. Apply this test to accounts payable, revenue transactions, and expense reports to identify anomalies warranting investigation. The technique works best with large datasets spanning several orders of magnitude.
Machine learning models offer sophisticated pattern recognition capabilities:
Prepare your data by cleaning, normalizing, and addressing missing values that could skew model training
Select appropriate algorithms based on your fraud scenario (classification for fraud/no fraud, clustering for anomaly detection)
Train models using historical data with known fraud cases to establish baseline patterns
Validate model performance using separate test datasets to ensure generalizability
Apply trained models to current period data to identify high-risk transactions or accounts
Investigate flagged items through traditional audit procedures to confirm or refute fraud indicators
Random Forest algorithms excel at handling complex, non-linear relationships in financial data. They create multiple decision trees and aggregate their predictions, reducing overfitting risk while maintaining high accuracy. XGBoost (Extreme Gradient Boosting) builds on this approach with enhanced performance through iterative error correction. Neural networks can identify subtle fraud patterns but require larger training datasets and more computational resources.
Method | Accuracy Rate | Interpretability | Best Use Case |
Benford’s Law | 70-80% | High | Initial screening of large transaction populations |
Random Forest | 90-95% | Medium | Complex fraud schemes with multiple risk factors |
XGBoost | 93-97% | Medium | High-stakes audits requiring maximum detection accuracy |
Neural Networks | 95-98% | Low | Organizations with substantial historical fraud data |
Pro Tip: Address data imbalance by using techniques like SMOTE (Synthetic Minority Over-sampling Technique) or adjusting class weights in your models. Fraud cases typically represent less than 5% of transactions, which can cause models to achieve high accuracy by simply predicting “no fraud” for everything. Balancing techniques ensure models learn to recognize actual fraud patterns rather than just predicting the majority class.
Maintaining model interpretability remains crucial for audit evidence. While complex models may achieve higher accuracy, you must explain why specific transactions were flagged to support audit conclusions. Consider using SHAP (SHapley Additive exPlanations) values or similar techniques to understand which features drove model predictions. This transparency helps you design targeted follow-up procedures and communicate findings effectively.
Integrating analytics into your audit workflow requires planning. Start with pilot projects on specific account areas before expanding to comprehensive implementation. Build relationships with IT personnel who can provide data extracts in usable formats. Document your analytical procedures, including model parameters and validation results, to support audit work papers. Organizations seeking to enhance their capabilities should explore detecting fraud using AI training focused on practical implementation in procurement processes.
Verifying findings and communicating fraud risks effectively
Preliminary fraud indicators require rigorous verification before reaching conclusions. Enhanced testing procedures tailored to suspected risks provide the evidence needed to confirm or refute initial findings. This verification phase separates false positives from genuine fraud, ensuring audit conclusions rest on solid evidentiary foundations.
Verification techniques depend on the nature of suspected fraud:
For revenue recognition issues, examine underlying contracts and delivery documentation to confirm transaction substance
When expense manipulation is suspected, trace payments to bank statements and verify vendor legitimacy through independent sources
For inventory fraud, conduct surprise physical counts and reconcile to perpetual records
If management override is indicated, expand testing of journal entries and accounting estimates with heightened skepticism
Enhanced testing goes beyond standard audit procedures in scope and depth. Rather than sampling, consider testing entire populations of flagged transactions. Interview multiple personnel to corroborate or contradict explanations. Obtain external confirmations from third parties to verify transaction details independently. This comprehensive approach provides the evidence quality needed when fraud risk is elevated.
The response phase includes enhanced testing and communication per auditing standards to address fraud risks effectively. Communication serves multiple purposes throughout the detection process. During fieldwork, discuss preliminary findings with appropriate management levels to understand context and obtain explanations. This dialogue may reveal legitimate business reasons for apparent anomalies or confirm suspicions warranting further investigation.
Formal communication follows established protocols:
Report significant fraud risks and related audit responses to those charged with governance
Communicate identified control deficiencies that increase fraud opportunity to management
When fraud is detected or suspected, inform appropriate levels of management and governance immediately
Document all communications in audit work papers, including dates, attendees, and key discussion points
Transparency in communication builds trust while fulfilling professional responsibilities. Clearly explain the nature of identified risks, their potential impact, and recommended remediation steps. Avoid technical jargon when communicating with non-audit stakeholders, focusing instead on business implications and actionable recommendations. This approach facilitates organizational response and demonstrates the value of thorough fraud detection procedures.
“Effective fraud communication balances professional skepticism with constructive dialogue. The goal is protecting the organization while maintaining productive working relationships that enable ongoing monitoring and improvement.”
Documentation completes the verification and communication cycle. Summarize your fraud risk assessment process, including identified risks, procedures performed, findings, and communications. This documentation supports audit opinions and provides a foundation for subsequent audits. Understanding compliance auditing and risk management connections helps position fraud detection within broader organizational governance frameworks.
Verification and communication transform preliminary indicators into actionable insights. This disciplined approach ensures fraud detection efforts produce reliable conclusions that stakeholders can use to strengthen controls and protect organizational assets.
Expand your expertise with specialized fraud detection training
Mastering fraud detection requires continuous learning as schemes evolve and detection technologies advance. Compliance-seminars.com offers comprehensive CPE training designed specifically for auditors and compliance professionals seeking to enhance their fraud detection capabilities. Our courses integrate current standards with practical techniques you can implement immediately in your audit practice.
Explore our 2026 CPE event calendar featuring live webinars and in-person seminars across multiple U.S. cities. These NASBA-recognized programs cover emerging fraud schemes, advanced analytics applications, and regulatory updates affecting fraud detection requirements. Learn from instructors with Big 4 backgrounds who bring real-world experience to every session.
Deepen your understanding through specialized offerings including risk assessment training that builds the foundation for effective fraud detection. Our fraud detection internal controls training provides hands-on experience designing and testing controls that prevent and detect corporate fraud. These practical programs equip you with frameworks and tools that elevate your professional capabilities and strengthen organizational defenses against fraud.
Frequently asked questions
How do auditors identify management override of controls as a fraud risk?
Auditors identify management override through inquiries with personnel at various organizational levels and analytical procedures examining unusual transactions or journal entries. This risk is presumed significant in every audit, requiring specific testing procedures regardless of control environment strength. Procedures include testing journal entries, reviewing accounting estimates for bias, and evaluating business rationale for significant unusual transactions.
What are the advantages of using machine learning in fraud detection?
Machine learning methods achieve accuracy exceeding 95% in detecting complex fraud patterns that traditional methods often miss. These algorithms identify subtle relationships across multiple variables simultaneously, uncovering schemes that manual analysis would overlook. However, some models face interpretability challenges, requiring auditors to balance accuracy gains with the need to explain findings clearly in audit documentation and stakeholder communications.
How can auditors ensure compliance with PCAOB and AICPA fraud standards?
Auditors ensure compliance by applying the prescribed four-phase risk assessment cycle of identification, assessment, response, and communication per AU-C 240 and AS 2401. Integrating these standards with COSO framework principles strengthens the overall approach by addressing control environment, risk assessment, control activities, information systems, and monitoring components. Regular training on standard updates and documentation of all fraud risk procedures demonstrate ongoing compliance commitment. Understanding the role of risk assessment helps auditors connect fraud detection procedures to broader audit strategy and regulatory requirements.
What data analytics tools are most effective for fraud detection?
Benford’s Law analysis provides an accessible starting point for identifying numerical anomalies in large transaction populations. Machine learning algorithms including Random Forest and XGBoost offer higher accuracy for complex fraud schemes involving multiple risk factors. The most effective approach combines multiple tools, using simpler techniques for initial screening and reserving sophisticated models for high-risk areas requiring deeper analysis.
How should auditors communicate suspected fraud to management?
Communicate suspected fraud promptly to appropriate management levels above those potentially involved, maintaining confidentiality to protect the investigation. Present factual findings without premature conclusions, explaining the procedures performed and evidence obtained. Recommend immediate steps to secure relevant documentation and prevent further loss while formal investigation proceeds. Document all communications thoroughly, including dates, attendees, information shared, and management responses for audit work papers.
Recommended
Comments