Forensic auditing explained: Investigative methods for detecting fraud
- John C. Blackshire, Jr.

- 2 minutes ago
- 8 min read

TL;DR:
Traditional audits are not designed to detect fraud; forensic audits focus on uncovering deliberate deception.
Forensic auditing involves comprehensive investigation phases, including evidence preservation, data analysis, and interviews.
Digital threats like management override and cryptocurrency laundering require advanced forensic skills, including blockchain analysis.
Most audit professionals assume that regular financial audits create a solid safety net against fraud. They do not. Organizations lose roughly 5% of annual revenue to fraud, with a median loss of $145,000 per incident. Traditional audits are built for accuracy and compliance, not for catching deliberate deception. Forensic auditing fills that gap. It uses investigative techniques, specialized data analysis, and legal-grade documentation to expose what standard audits routinely miss. This article walks you through the core methodologies, real-world applications, and emerging challenges every audit and compliance professional needs to understand.
Table of Contents
Key Takeaways
Point | Details |
Forensic audits are investigative | They go beyond routine checks to examine all relevant data and uncover specific fraud or misconduct. |
Fraud is persistent and costly | Organizations typically lose 5% of annual revenue to fraud, highlighting the need for specialized detection. |
Methodologies are multifaceted | Effective forensic audits leverage planning, evidence handling, data analytics, interviews, and clear reporting. |
Modern risks require new tools | Digital forensics and AI analytics are essential for detecting cryptocurrency misuse and management override. |
Continuous learning is crucial | Ongoing training and professional skepticism distinguish successful forensic auditors. |
How forensic auditing differs from traditional audits
Understanding the distinction between a traditional financial audit and a forensic audit is not just academic. It shapes how you plan your work, gather evidence, and report findings.
A traditional audit is designed to provide reasonable assurance that financial statements are materially accurate. Auditors use sampling, apply materiality thresholds, and follow a structured framework like GAAS or PCAOB standards. The goal is an opinion on financial statement fairness, not a verdict on wrongdoing.
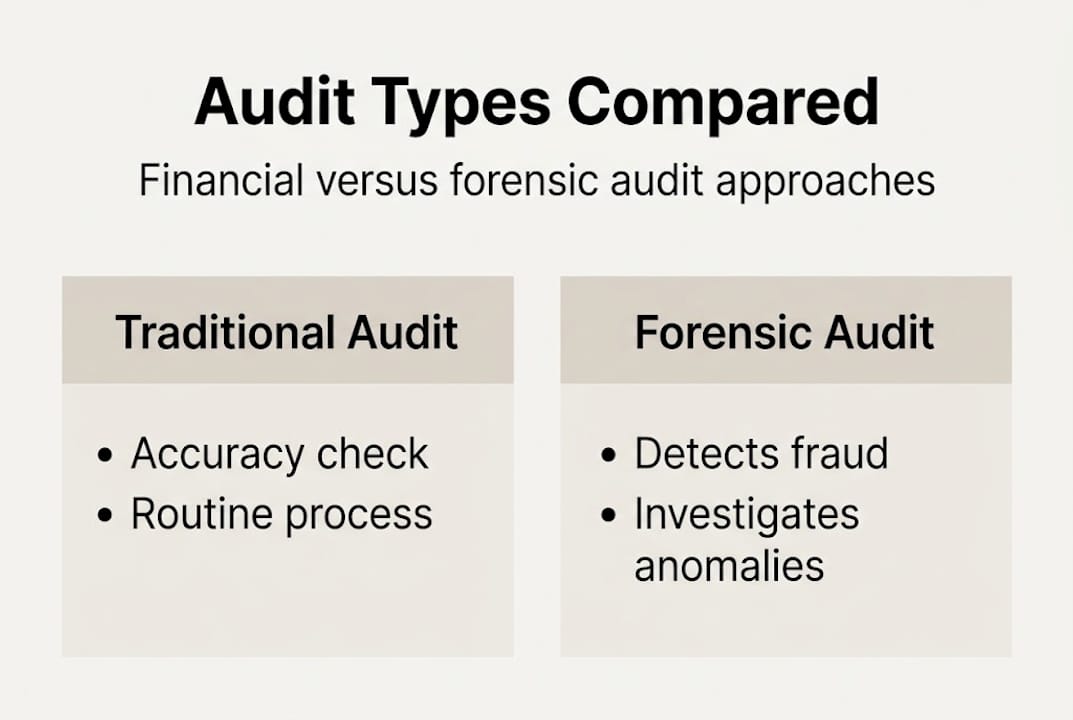
Forensic auditing operates on a different premise entirely. It is triggered by suspicion, a tip, a regulatory referral, or an anomaly that cannot be explained. As noted in audit vs. forensic accounting, forensic audits are investigative, examining all relevant data without materiality thresholds, whereas traditional audits focus on material accuracy via sampling. Every transaction can be relevant. Every document is potentially evidence.
Here is a side-by-side comparison to make the differences concrete:
Feature | Traditional audit | Forensic audit |
Purpose | Financial statement accuracy | Fraud detection and investigation |
Scope | Sampled, material items | All relevant transactions |
Trigger | Scheduled, recurring | Suspicion, allegation, or incident |
Output | Audit opinion | Investigative report for legal use |
Standards | GAAS, PCAOB | Legal evidentiary standards |
Materiality | Applied | Not applicable |
Key characteristics that set forensic audits apart include:
No materiality filter. Small transactions are scrutinized if they appear suspicious.
Legal admissibility. Evidence must be gathered and preserved in a way that holds up in court.
Investigative mindset. The auditor approaches the work with professional skepticism from the first step.
Cross-functional scope. Forensic auditors often work alongside legal counsel, law enforcement, and IT specialists.
“The forensic auditor is not just checking numbers. They are building a case.”
If you are new to the investigative side of audit work, reviewing a solid fraud examination guide can help bridge the gap between traditional audit thinking and forensic methodology.
Core methodologies in forensic auditing
Knowing that forensic auditing is different is one thing. Knowing how it actually works is what makes you effective in the field. The process is disciplined and sequential, with each phase building on the last.
Key methodologies include planning and scoping the investigation, evidence preservation, data analytics like Benford’s Law, transaction testing, fund tracing, interviews, and detailed reporting. Here is how each phase plays out:
Planning and scoping. Define the allegations, identify key parties, and establish the boundaries of the investigation. A poorly scoped forensic audit wastes time and risks missing critical evidence.
Evidence preservation. Secure financial records, emails, system logs, and physical documents immediately. Chain of custody, meaning a documented record of who handled evidence and when, is non-negotiable for legal proceedings.
Data analytics. Apply tools like Benford’s Law (a statistical test that flags unusual digit patterns in financial data), trend analysis, and ratio analysis to identify anomalies at scale.
Transaction testing. Trace specific transactions from initiation through approval, payment, and recording. Look for missing approvals, duplicate payments, or unusual vendor relationships.
Fund tracing. Follow the money through bank accounts, wire transfers, and third-party entities to identify where funds went.
Interviews. Conduct structured interviews with employees, management, and third parties. Sequence matters: interview peripheral witnesses before key suspects.
Reporting. Document findings clearly, with supporting evidence, for potential use in legal proceedings, regulatory submissions, or management action.
Pro Tip: Always maintain a detailed investigation log. Note every action, every document reviewed, and every conversation. Courts and regulators will scrutinize your process as closely as your findings.
Phase | Primary tool | Key output |
Planning | Risk assessment | Investigation scope document |
Evidence preservation | Chain of custody protocol | Secured evidence file |
Data analytics | Benford’s Law, ACL, IDEA | Anomaly report |
Transaction testing | Vouching, tracing | Exception list |
Reporting | Forensic report template | Legal-grade findings document |
For professionals looking to build these skills formally, investigative accounting training and a dedicated forensic accounting event offer structured, CPE-eligible instruction grounded in real case scenarios.
Detecting and preventing fraud: Practical applications
Methodology only matters when it produces results. Here is how forensic auditing translates into actual fraud detection and prevention across organizations.
According to ACFE 2024/2025 data, asset misappropriation is the most common fraud scheme, representing the majority of cases. The median organizational loss sits at $145,000, and most schemes run for about 12 months before anyone notices. That is a full year of losses before detection.
The most common fraud types forensic auditors encounter include:
Asset misappropriation. Theft of cash, inventory, or company assets by employees.
Billing fraud. Fictitious vendors, inflated invoices, or payments to shell companies.
Payroll fraud. Ghost employees, inflated hours, or unauthorized commission payments.
Expense reimbursement fraud. Personal expenses submitted as business costs.
Financial statement fraud. Manipulation of reported revenues, expenses, or assets.
Tips and whistleblowers remain the primary detection method, accounting for more fraud discoveries than any audit procedure. This tells us something important: your control environment and reporting culture matter as much as your technical methods.
Pro Tip: Build a proactive forensic audit program rather than waiting for an allegation. Scheduled forensic reviews of high-risk areas like accounts payable, expense reports, and payroll can surface issues before they become material losses.
Understanding the fraud detection process in depth, and knowing how to spot red flags of fraud early, gives your organization a measurable advantage. Professionals who want to go further can explore formal accounting for fraud training to sharpen their investigative judgment.
Emerging challenges: Management override and digital threats
Traditional fraud schemes are well-documented and increasingly detectable. The harder problem is what happens when controls are bypassed deliberately or when fraud moves into digital spaces that most auditors are not yet equipped to navigate.

Management override of controls is one of the most stubborn challenges in forensic auditing. When senior leaders circumvent established controls, they often leave few obvious traces. Over 50% of cases involve management override, with higher losses concentrated in smaller firms where segregation of duties is weaker and oversight is less formal.
Cryptocurrency adds another layer of complexity. 47% of cases now involve cryptocurrency use for laundering, making traditional fund tracing methods insufficient on their own. Blockchain analysis tools are becoming a required competency, not an optional add-on.
Key emerging threats forensic auditors must address include:
Management override. Requires tone-at-the-top assessments, board-level oversight, and journal entry testing.
Cryptocurrency laundering. Demands blockchain forensics tools and knowledge of wallet tracing techniques.
AI-generated fraud. Deepfakes, synthetic identities, and automated phishing schemes are increasing in sophistication.
Cloud data complexity. Evidence may reside across multiple jurisdictions, platforms, and vendors, complicating preservation and access.
“The forensic auditor of 2026 needs to be part accountant, part data scientist, and part digital investigator.”
Digital forensics and AI-driven analytics are now essential tools in the modern forensic auditor’s toolkit. If your team’s digital skills have not kept pace with the threat landscape, reviewing cybersecurity audit tools is a practical starting point.
Beyond best practices: What most forensic audit guides overlook
Most guides on forensic auditing focus on process. Follow the steps, use the right tools, document everything. That framework is necessary, but it is not sufficient.
Here is what we have seen consistently across real investigations: no two fraud scenarios are alike. The scheme that worked in a manufacturing company looks completely different in a nonprofit or a financial institution. Context shapes everything, from how you scope the investigation to which red flags actually matter.
The best forensic auditors we know are not just technically skilled. They are deeply skeptical in a productive way. They ask why a process exists, not just whether it was followed. They notice when an explanation is technically accurate but feels incomplete. That kind of professional skepticism, grounded in the role of ethics in auditing, is what separates a competent auditor from an exceptional investigator.
Cross-disciplinary knowledge matters too. Understanding behavioral psychology, legal standards for evidence, and basic IT architecture makes you far more effective than someone who only knows the accounting side. Continuous education is not a checkbox. It is how you stay relevant as fraud evolves.
Advance your forensic auditing skills
Forensic auditing is a discipline that rewards depth. The more you understand about investigative methodology, fraud psychology, and digital evidence, the more effective you become at protecting your organization and your clients.
At compliance-seminars.com, we offer targeted training designed specifically for audit and compliance professionals. Whether you prefer CPE webinars for auditors or structured in-person instruction, our curriculum covers forensic accounting, fraud investigation, and digital audit techniques. Explore our forensic accounting seminar for hands-on, case-based learning, or browse the full CPE event calendar to find upcoming sessions in your area. Every course is NASBA-recognized and built for working professionals.
Frequently asked questions
How is forensic auditing different from internal auditing?
Forensic auditing is investigative and focused on uncovering fraud or misconduct, while internal auditing reviews controls and processes for accuracy and compliance. Forensic audits examine all data without materiality limits, whereas internal audits typically apply risk-based sampling.
What are the most common fraud schemes detected by forensic audits?
Asset misappropriation is the most frequent scheme detected, followed by corruption and financial statement fraud. These schemes often run undetected for months before a tip or anomaly surfaces them.
What digital tools are essential for modern forensic auditors?
Key tools include data analytics platforms like ACL and IDEA, AI-based anomaly detectors, and digital forensics technology for tracing cryptocurrencies. AI analytics and digital forensics are now required competencies given the rise of cryptocurrency-based laundering schemes.
How long do fraud schemes typically go undetected?
Most schemes last a median of 12 months before discovery, with tips and whistleblowers being the most common detection method. Proactive forensic reviews can significantly shorten that window.
Recommended
Comments